On Wednesday, April 29, 2026, the security team at Theori disclosed a new Linux kernel bug—they dubbed it Copy Fail (CVE-2026-31431). Most of the chatter focuses on corporate servers and clouds. But that same kernel powers your home setup too—Raspberry Pi running Raspberry Pi OS (formerly Raspbian), Home Assistant Yellow/Green/Blue, HAOS on a NUC, or NAS. And in a homelab, Copy Fail hits where the cloud talk glosses right over it.
Short version: On a vulnerable device, an unprivileged user can snag full root access in seconds with a 732-byte Python script. No dependencies, no fancy exploit chain. The flaw’s been lurking in the kernel since 2017, hitting every modern Linux distro.
Why You Should Care
This bug alone won’t let an attacker break in from the outside—they need an existing account on the device to exploit it. That’s the catch.
If you’ve got anything exposed to the internet on your Raspberry Pi, NAS or Home Assistant—the Home Assistant frontend itself, OctoPrint, Pi-hole admin panel, Nextcloud, Vaultwarden, or some web app you hacked together (or vibecoded with AI)—and that app has a security hole, the attacker gets in via the app’s account. Before, that’d be it. They’d only touch that one service’s data. With Copy Fail, they escalate to root on the whole device in moments.
Root means everything—all your data, keys, passwords, plus a foothold into the rest of your home network where the device’s connected. If Home Assistant itself is the compromised app, the attacker also grabs control over everything HA manages—smart locks, alarms, heating, cameras.
Docker Won’t Save You Either
If you’re counting on Docker containers for isolation from the host, think again. Copy Fail lets an attack escape from the container to the host—they share the same kernel and memory. A proof-of-concept via container popped up on GitHub a day after disclosure. Same deal for Docker on your Pi.
What to Do About It
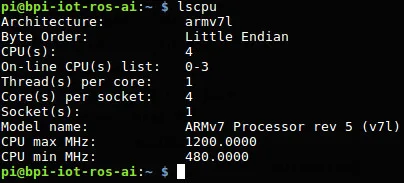
What isn’t affected: ESP32, ESP8266, RP2040, STM32 (no Linux, no problem), plus cameras, routers, smart home hubs, and similar gear with specialized firmware. That stuff usually runs older kernels or ones without the vulnerable bits—Copy Fail skips them.
For vulnerable devices, three practical steps:
- Update now. Run
sudo apt update && sudo apt full-upgrade, or use the HAOS update interface, and watch for kernel patches in your distro. They’re rolling out across distributions. - Hide non-public stuff behind a VPN (Tailscale, WireGuard). If you don’t need Pi-hole admin or OctoPrint accessible from anywhere, no reason to expose them. Watch out for cloudflared tunnels too—without Cloudflare Access authentication, you’re just exposing the app differently online, and it won’t shield you from exploits in the app itself.
- For your own (vibecoded) apps, ask if they really need a public IP. Security in that kind of code is tricky enough on its own, and Copy Fail turns a minor app flaw into full machine takeover.
Detailed tech steps (like quickly disabling the affected kernel module before an official patch drops, or service hardening tips) are in the links below.
Background pulled together by Czech maker/security researcher Vláďa Smitka (source)
Links: Theori writeup on Xint, CERT-EU advisory, copy.fail, Sysdig analysis.